Approval policy»
Approval policies allow organizations to create sophisticated run review and approval flows that reflect their preferred workflow, security goals, and business objectives. Without an explicit approval policy, anyone with write access to a stack can create a run or task. An approval policy can make this process more granular and contextual.
Runs can be reviewed by approval policies when they enter one of three states: queued, unconfirmed, or pending review. If a stack has autodeploy enabled, then the approval policy will not be evaluated here, and you should use a plan policy to warn, which will force the stack into an unconfirmed state, at which point the approval policy will get evaluated as a safeguard.
When a queued run needs approval, it will not be scheduled until that approval is received. If the run is of a blocking type, it will block newer runs from scheduling too. A queued run that's pending approval can be canceled at any point.
Review a run»
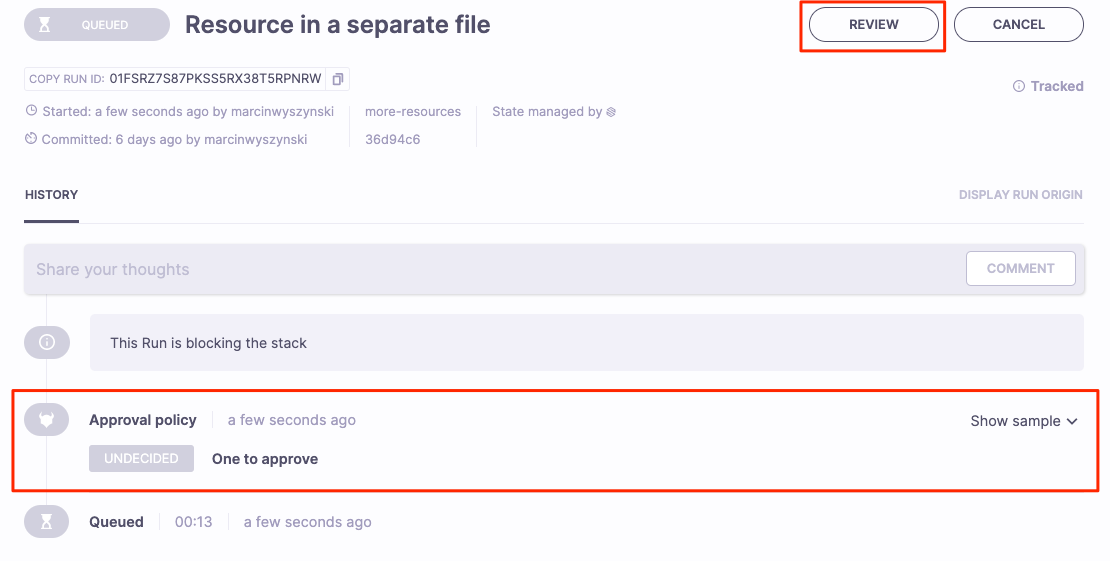
In this example, a queued run is waiting for a human review, and the last approval policy evaluation returned an Undecided decision.
- Navigate to the Ship Infra > Runs tab and select the run that needs review.
- You can also access runs for a specific stack by navigating to the Stacks tab, clicking the name of the stack, and clicking the run to review in the Tracked Run section.
- Click Review in the top right.
- Review the changes, then click Approve if the run can continue, or Reject if the run should be canceled.
- If desired, you can leave a comment from your review in the text box.
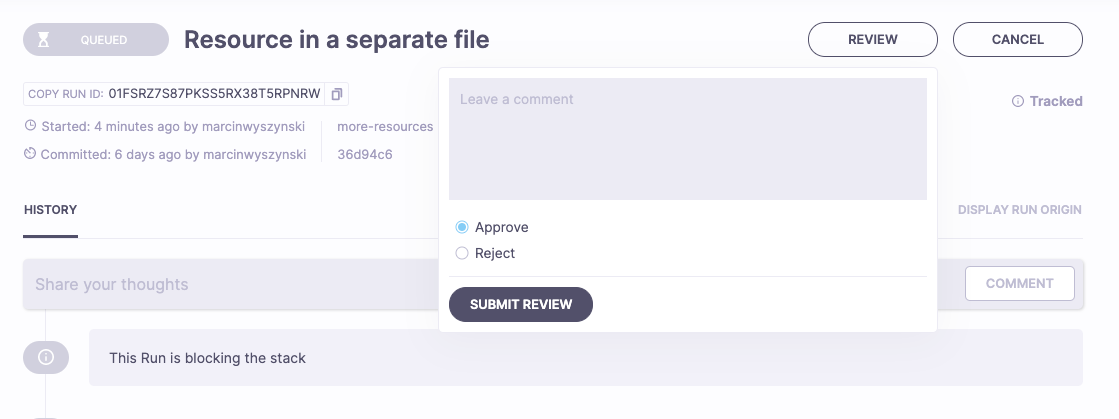
- If desired, you can leave a comment from your review in the text box.
- Click Submit Review.
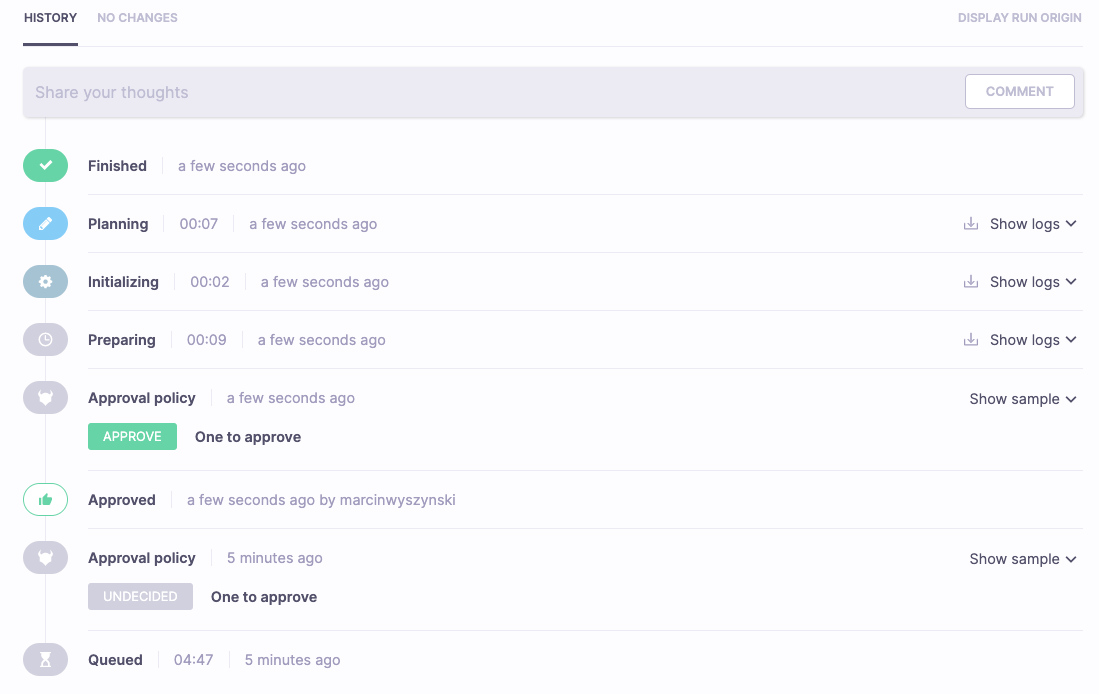
- If you approved the run, the approval policy will evaluate to Approved, thus unblocking the run.
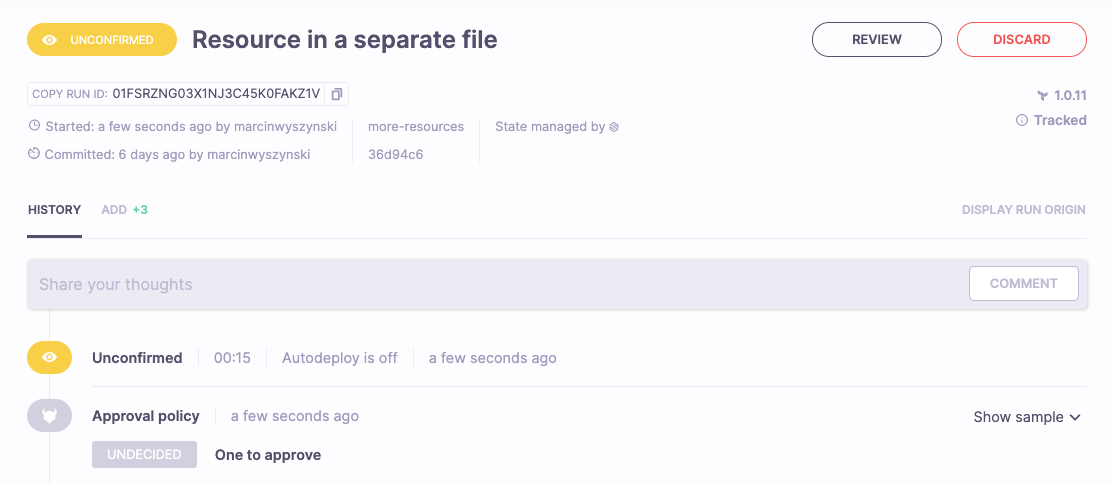
When an unconfirmed run needs approval, you will not be able to confirm it until that approval is received. The run can, however, be discarded at any point:
The run review and approval process is very similar to GitHub's Pull Request review. The only exception is that it's the Rego policy (rather than a set of checkboxes and dropdowns) that defines the exact conditions to approve the run.
Tip
If separate run approval and confirmation steps sound confusing, think about how GitHub's Pull Requests work. You can approve a PR before merging it in a separate step. A PR approval means "I'm ok with this being merged", while a run approval means "I'm OK with that action being executed".
Rules»
Your approval policy can define the following boolean rules:
- approve: The run is approved and no longer requires (or allows) review.
- reject: The run fails immediately.
While the approve rule must be defined in order for the run to be able to progress, you don't need to define the reject rule. If reject rules are undefined, runs that look invalid can be canceled or discarded manually.
Any given policy evaluation can also return false on both approve and reject rules. This only means that the result is yet undecided, and more reviews will be necessary. A perfect example would be a policy that requires 2 approvals for a given job; the first review is not supposed to set the approve value to true.
How it works»
When a user reviews the run, Spacelift persists the review and passes it to the approval policy (along with other reviews), plus some information about the run and its stack.
The same user can review the same run as many times as they want, but only their newest review will be presented to the approval policy. This mechanism allows you to change your mind, very similar to Pull Request reviews in GitHub.
Data input schema»
This schema is an informational example, as JSON doesn't support comments by design. You can play with this sample (and others) using the policy workbench or policy templates.
Each approval policy request will receive this data input schema:
Official Schema Reference
For the most up-to-date and complete schema definition, please refer to the official Spacelift policy contract schema under the APPROVAL policy type.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 | |
Approval policy examples»
These policy examples can be imported directly into your Spacelift.
Tip
We maintain a library of example policies ready to use or alter to meet your specific needs.
If you cannot find what you are looking for below or in the library, please reach out to our support and we will craft a policy to do exactly what you need.
Two approvals, no rejections»
In this example, each Unconfirmed run (including proposed runs triggered by Git events) will require two approvals. Additionally, the run should have no rejections. Anyone who rejects the run will need to go back and approve it in order for the run to go through.
Info
We suggest requiring more than one review because one approval should come from the run/commit author to indicate that they're aware of what they're doing, especially if their VCS handle is different than their IdP handle. This is something we practice internally at Spacelift.
1 2 3 4 5 6 7 8 | |
1 2 3 4 5 6 7 8 | |
Two to approve, two to reject»
This is a variation of the above policy that will automatically fail any run that receives more than one rejection.
1 2 3 4 5 | |
1 2 3 4 5 | |
Require approval for a task command not on the allowlist»
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 | |
1 2 3 4 5 6 7 8 9 10 11 12 | |
Options for input.run.type include PROPOSED, TRACKED, TASK, TESTING, DESTROY.
Combining multiple rules»
Usually, you will apply different rules to different types of jobs. Since approval policies are attached to stacks, you'll want to be smart about how you combine different rules. Here's how you can combine two of the above approval flows as an example:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 | |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 | |
Role-based approval»
Sometimes you want to give specific roles (but not others) the power to approve certain workloads. The policy below approves an unconfirmed run or a task when either a Director approves it, or both DevOps and Security roles approve it:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 | |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 | |
Require private worker pool»
You might want to ensure that your runs are always scheduled on a private worker pool. You could use an approval policy similar to this ones:
1 2 3 4 5 6 7 | |
1 2 3 4 5 6 7 | |
You may want to auto-attach this policy to some, if not all, of your stacks.
Use more descriptive approvals»
Sometimes it is worth adding notes about approval/rejection to see why without Rego code analysis.
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 | |
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 | |